In this Raspberry Pi MAC address spoofing tutorial, we will be showing you how you can spoof the MAC Address of your Raspberry Pi’s network interfaces, either setting it to a known different MAC address or randomly generating it on the fly.

This tutorial is split into two different sections. The first section shows you how you can easily spoof the Raspberry Pi’s inbuilt ethernet ports MAC address by modifying the cmdline.txt file.
The second section shows you how you can take this a step further utilizing the macchanger tool to change the MAC address of any of your network interfaces.
Spoofing your MAC address can be handy for numerous different reasons, one of these might be to try and retain your device’s privacy so you can’t just be tracked based off your MAC Address.
Another reason might be that you want to use the Raspberry Pi as a direct replacement for an older Pi and want it to retain the same MAC Address.
You can find the full tutorial on how to set up Raspberry Pi MAC address spoofing below.
Equipment
Below is the full list of equipment that you will need to complete this tutorial.
Recommended
Optional
Spoofing the Raspberry Pi’s Ethernet MAC Address
1. Spoofing your Raspberry Pi’s Ethernet MAC address is an incredibly simple task, especially in comparison to doing this for a WiFi connection.
Spoofing the ethernet MAC address involves utilizing an override that you can set through the cmdline.txt file. This change will prevent the system from just using the default address.
Now there are two different ways that you can modify the cmdline.txt file. One is to take out your SD Card from your Raspberry Pi and plug it into your computer. The other is to edit it on the Pi itself.
We recommend taking out the SD Card when changing something like the Raspberry Pi’s MAC Address.
If you have inserted your SD Card into your computer you should find the cmdline.txt file on the root of your SD Card, open it in your favorite plain text editor.
However, if you decide to edit this file on the Raspberry Pi, you can utilize the following command to begin editing it.
sudo nano /boot/cmdline.txt2. Within this file, you will find one single line of text with a dozen different options set in it.
To the very end of the line, we want to add the following text, make sure you replace the example MAC Address (XX:XX:XX:XX:XX:XX) with your desired one before continuing.
This text is what will tell the system what MAC address to utilize for the ethernet port.
smsc95xx.macaddr=XX:XX:XX:XX:XX:XX3. Once you have made the change to the file, save it. If you are using nano, you can save the file by pressing CTRL + X then Y and finally ENTER.
You will now need to either plug back in your SD Card into your Raspberry Pi or if you edited the file directly you will now need to reboot the device.
If you are editing your Raspberry Pi’s MAC address directly on the device, then reboot with the following command.
sudo reboot4. You can now verify whether you have successfully spoofed your Raspberry Pi’s MAC Address by running the following command on it. This command will bring up all the information about your ethernet network adapter.
sudo ifconfig eth05. If everything has now worked as it should have you should now be able to find your custom, spoofed MAC address displayed on the screen.
For example, if you just used XX:XX:XX:XX:XX:XX you should see a line similar to what we have displayed below.
ether XX:XX:XX:XX:XX:XX txqueuelen 1000 (Ethernet)Spoofing the Raspberry Pi’s Network MAC Address
1. As always when first doing a tutorial, we should first ensure that our Raspberry Pi’s operating system is entirely up to date by running the following two commands.
sudo apt update
sudo apt upgrade2. In addition to updating all the available packages, we need to go ahead and upgrade the Raspberry Pi’s firmware. We do this as some models had issues with the MAC addresses being modified that was fixed in a firmware update.
To update the Raspberry Pi’s firmware run the following command, make sure your Raspberry Pi does not lose power while this runs.
sudo rpi-update3. To get the Raspberry Pi to utilize this updated firmware, we need to now restart the Raspberry Pi by running the following command.
sudo reboot4. The easiest way to spoof the MAC address for other network devices such as your WiFi is to utilize a program called macchanger. This program handles all the grunt work with modifying and spoofing the MAC address of the network devices.
We can install this program to our Raspberry Pi easily by running the following command.
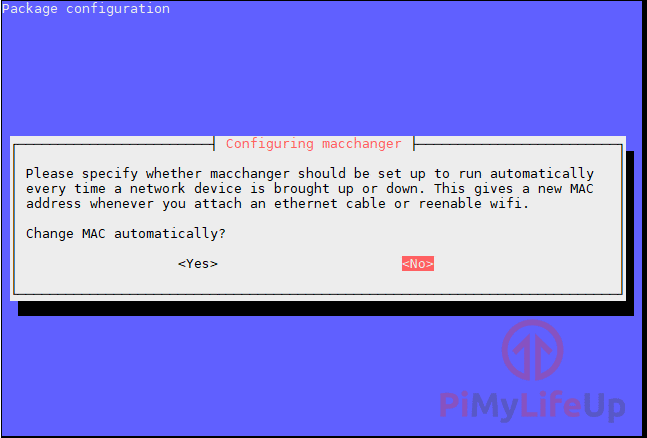
sudo apt install macchanger5. During the installation process of macchanger, you will be asked if you want it to automatically generate new MAC addresses every time a network device is brought up
This, of course, will mean you will not be able to predict what the MAC address will be, but if this is the behavior you want, select <YES>.
For this tutorial, we will be selecting <NO>.
6. With macchanger now installed to our Raspberry Pi, we can proceed on to utilizing it.
To start let’s first get a list of all currently up network interfaces. We can do that by utilizing the ifconfig program with the following command.
ifconfig7. From that list of network interfaces, pick the one you intend on spoofing the MAC address for.
Whichever it is make sure you are not currently connected over SSH as this process will temporarily bring that device offline.
For our tutorial, we will be modifying the MAC address of our wlan1 device, replace wlan1 in the next command with the network interface you want to change.
sudo ifconfig wlan1 down8. Now that we have brought down the interface we can go ahead and utilize the macchanger software to modify its MAC address.
There are two ways to do this. We can either specify the MAC address that we want to utilize or tell the software to generate a random one for it.
Follow step 8a if you want to generate a random spoofed MAC address, otherwise follow step 8b to see how you can specify your own MAC address.
8a. We will assign a random new MAC address to our network interface by using the -r argument of macchanger. (There is also the -e argument that gives it a somewhat random MAC address by generating it based on the same vendor name)
sudo macchanger -r wlan18b. If you want to specify your own MAC address, you can utilize the -m argument alongside your MAC address. Make sure you replace XX:XX:XX:XX:XX:XX with the mac address you want to use.
sudo macchanger -m XX:XX:XX:XX:XX:XX wlan19. Using either one of these commands should give you a result as we have shown below. With it specifying the current MAC address and the new one that you either just generated or specified.
pi@raspberrypi:~ $ sudo macchanger -r wlan1
Current MAC: 00:c1:41:07:11:74 (unknown)
Permanent MAC: 00:c1:41:07:11:74 (unknown)
New MAC: 1e:c7:73:41:5f:40 (unknown)10. Now that we have learned how we can spoof the MAC address for any of our network interfaces there is one last thing we need to do, and that is to make these changes take effect on the system boots up.
To do this, we need to create a file within the /etc/network/if-up.d folder by running the following nano command. The files within this directory are called when a network interface is brought online.
sudo nano /etc/network/if-up.d/macchange11. To this file, we need to add the following lines of script, when you come to the macchanger line make sure that you change this to reflect what you want it to do.
For instance to use -r if you intend on just randomizing the MAC Address or utilizing -m if you want to specify your own.
You can change as many MAC addresses from within this script as the file is only called.
#!/bin/sh
if [ "$IFACE" = lo ]; then
exit 0
fi
/usr/bin/macchanger -m 02:c9:91:54:f6:06 wlan112. Finally, save the file by pressing CTRL + X then Y and finally ENTER.
13. Next, we need to make the script executable by using the chmod command.
sudo chmod 755 /etc/network/if-up.d/macchange14. Let’s test to ensure everything is working as it should be restarting the Raspberry Pi with the following command.
sudo reboot15. Once your Raspberry Pi has finished rebooting you will be able to check your network interfaces current MAC address by running the following command.
Replace wlan1 with the network interface that you are utilizing.
macchanger wlan116. If everything is working as it should be, you should now see that your Current MAC differs from your Permanent MAC as we have showcased below.
Current MAC: 02:c9:91:54:f6:06 (unknown)
Permanent MAC: 00:c1:41:07:11:76 (unknown)At this point, you should now have your Raspberry Pi automatically spoofing the MAC address for your desired network interface on startup.
Conclusion
I hope by the end of this tutorial you will have learnt how to spoof the MAC address on your Raspberry Pi on either the Ethernet connection or any other network device such as your wireless connection.
There are plenty of other network projects that you can do on the Raspberry Pi that you might be interested in.
If you have any feedback on this MAC address spoofing tutorial, then please feel free to leave us a comment below.





This may help others…
Creating the file in /etc/network/if-up.d did not work for me (piping the output to a file revealed the following: [ERROR] Set device name: No such device).
I was able to get it to work by:
1) RUN sudo crontab -e
2) ADD AT BOTTOM @reboot macchanger -m 02:c9:91:54:f6:06 wlan1
3) Save and exit the editor
4) Reboot (sudo reboot)
You forgot to make the new script executable with “chmod 755 /etc/network/if-up.d/macchange”
Thanks for letting us know, we have updated the tutorial now.
Hi,
thanks for the tutorial, i have a little point. You have make the script executable with
sudo chmod +x /etc/network/if-up.d/macchange
before, the script cannot be executed.
Thanks Alex, we have updated the tutorial so the script will be made executable.